-
Type:
Problem report
-
Resolution: Fixed
-
Priority:
Trivial
-
Affects Version/s: 5.0.4, 5.0.5
-
Component/s: Agent (G)
-
None
-
Environment:Windows Server 2008 R2 (Russian)
-
Sprint 70 (Nov 2020), Sprint 71 (Dec 2020)
-
0.5
Steps to reproduce:
- Install Zabbix Agent2 and keep service's account as "Local System"
- Allow remote execution at Agent2 configuration file: AllowKey=system.run[*]
- Set logging debug level to 4
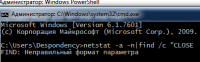
- Add as templtated or direct item key (unsigned): system.run[netstat -a -n|find /c "CLOSE"]
- Wait for result or push it manually
- See "▒▒▒ ▒▒▒▒㯠: \" in Agent's log (in Russian: "Нет доступа: \", in English: "Access denied: \"
Note: if i remove part, starting from "|" symbol from item key system.run[netstat -a -n|find /c "CLOSE"] (as system.run[netstat -a -n]), i get result (but without filtering via console command "find"). Any try to add "|" symbol to command make an error in output.
Possible affected to system.run[] with powershell and "|" used in expressions too (not tested).
Result:
See screenshot run_1 with combined server console and agent2 log file
Expected:
Unsigned number (from 0 to any other)
- duplicates
-
ZBX-18730 Zabbix Agent2 5.2.x on Windows UserParameter Error
-
- Closed
-